➤Summary
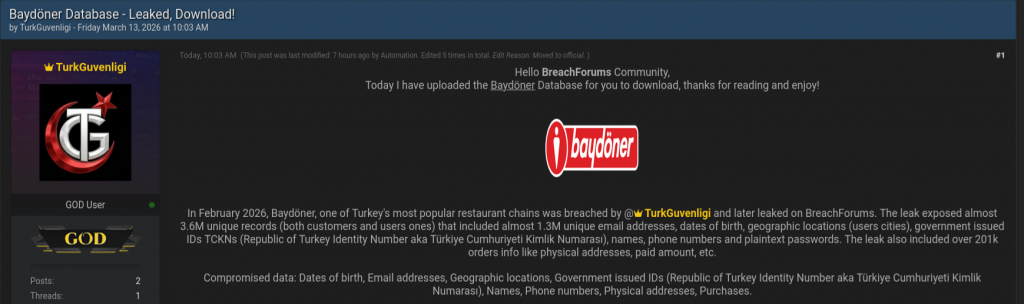
Baydöner data breach reports have emerged after threat actors allegedly published sensitive customer information on Breachforums.as in February 2026. According to findings shared by cybersecurity researchers, the incident involves one of Turkey’s most recognized restaurant chains, raising concerns about consumer privacy and retail cybersecurity practices. The discovery was made by the Kaduu team during routine monitoring of dark web forums, where a user known as TurkGuvenligi claimed access to a large database containing personal and transactional records.
While the breach remains unconfirmed officially, the scope of exposed information suggests potential identity theft risks and targeted fraud campaigns. Similar to recent restaurant-sector incidents worldwide, including the HungryRush exposure analyzed previously, this case highlights how food service platforms have become attractive targets for cybercriminal ecosystems. 🍽️
What We Know About the Alleged Incident
The database listing appeared on Breachforums.as, a well-known underground marketplace where threat actors frequently advertise stolen datasets. The alleged breach date is February 2026, with claims indicating extensive customer profiling data.
According to the forum post, compromised information includes:
- Full names
- Dates of birth
- Email addresses
- Phone numbers
- Physical addresses
- Geographic locations
- Purchase histories
- Government-issued IDs (Türkiye Cumhuriyeti Kimlik Numarası)
This combination dramatically increases fraud risks because identity documents paired with contact data enable account takeover attempts and social engineering attacks. Cybersecurity analysts often consider such datasets “high exploitation value” due to their completeness. 🔍
Types of Data Allegedly Exposed
Understanding the structure of leaked data helps organizations evaluate real-world consequences. Below is a simplified classification:
| Data Category | Risk Level | Potential Abuse |
| Identity Numbers | Critical | Identity theft |
| Emails & Phones | High | Phishing campaigns |
| Addresses | High | Targeted scams |
| Purchase Records | Medium | Behavioral profiling |
| Birth Dates | High | Account recovery abuse |
| This exposure resembles patterns observed in other hospitality breaches, where customer loyalty and ordering systems become entry points into larger databases. | ||
| Security researchers emphasize that attackers increasingly monetize consumer datasets through resale and credential-stuffing operations. 💻 |
How the Breach Was Discovered
The Kaduu team identified the alleged database during proactive monitoring of underground communities. Dark web intelligence operations often track keywords linked to brands, leaked credentials, and corporate assets.
This monitoring process allows analysts to detect threats before widespread exploitation occurs. Early detection enables companies to initiate containment strategies and begin incident response procedures even before attackers weaponize the data.
Experts note that many organizations only learn about breaches weeks after exposure unless continuous monitoring mechanisms are in place.
Why Restaurant Chains Are Growing Cyber Targets
The food and hospitality industry has undergone rapid digital transformation. Online ordering platforms, loyalty programs, and mobile payment integrations create large centralized customer databases.
Attackers target restaurants because:
- High transaction volume
- Large consumer datasets
- Often weaker cybersecurity maturity
- Multiple third-party integrations
- Cloud-based ordering systems
These conditions mirror trends highlighted in the HungryRush incident analysis published earlier on SpoofGuard, showing how customer engagement platforms can unintentionally expand attack surfaces.
Potential Risks for Customers
If confirmed, affected individuals could face several threats:
- Identity theft using national identification numbers
- Spear-phishing campaigns impersonating brands
- Financial fraud attempts
- SIM-swap attacks
- Targeted scam messaging
Question: Why are identity numbers especially dangerous when leaked?
Answer: Because they enable attackers to bypass identity verification processes used by banks, telecom providers, and government services.
This elevates risk beyond simple email exposure and moves into long-term identity compromise scenarios. ⚠️
Connection to Broader Data Breach Trends
The alleged Baydöner incident reflects a broader shift toward consumer-data monetization within cybercrime markets. Attackers increasingly bundle restaurant, retail, and service datasets to build detailed digital identities.
Industry reports show three major evolving trends:
- Credential aggregation marketplaces
- Data enrichment through multiple breaches
- Automated phishing infrastructure
Security professionals warn that breaches rarely exist in isolation; instead, datasets are merged to amplify attack effectiveness.
According to IBM’s Cost of a Data Breach research, stolen personal data remains one of the most profitable cybercrime assets globally:
https://www.ibm.com/reports/data-breach
This economic incentive explains why hospitality brands are repeatedly targeted. 📊
Organizational Security Lessons From the Incident
Even alleged breaches provide valuable defensive insights. Companies managing large customer databases should prioritize:
- Access control audits
- Encryption of identity records
- Vendor risk management
- Continuous monitoring
- Threat intelligence correlation
Preventive cybersecurity is no longer optional but operationally critical.
Organizations also benefit from integrating domain spoofing protection to reduce impersonation campaigns that typically follow major breach disclosures.
Practical Checklist for Businesses
Here is a quick defensive checklist organizations can apply immediately:
✅ Monitor dark web marketplaces regularly
✅ Implement multi-factor authentication
✅ Audit database permissions quarterly
✅ Monitor abnormal login behavior
✅ Deploy breach notification workflows
✅ Conduct employee phishing awareness training
These proactive steps significantly reduce exploitation windows following data exposure. 🛡️
The Role of Dark Web Monitoring and Intelligence
Modern cybersecurity strategies increasingly rely on intelligence-led defense. Analysts track underground forums to detect early warning signals before attacks scale.
Tools combining threat intelligence with automated alerts help security teams identify:
- Brand impersonation attempts
- Credential leaks
- Marketplace listings
- Fraud campaigns
Expert Insight
A cybersecurity analyst involved in breach monitoring stated:
“Data exposure today is less about if and more about how quickly organizations detect and respond.”
This reflects the shift from reactive security toward predictive defense models powered by intelligence analysis.
Long-Term Impact on Brand Trust
Consumer trust is often the most significant casualty of a breach allegation. Even unverified claims can influence customer perception and purchasing behavior.
Key reputational impacts include:
- Reduced customer loyalty
- Increased regulatory scrutiny
- Higher compliance costs
- Marketing recovery expenses
Transparency and rapid communication remain essential to rebuilding trust following disclosure events. 📣
How Customers Can Protect Themselves
Individuals potentially affected should take precautionary steps:
- Monitor financial statements
- Change reused passwords immediately
- Enable multi-factor authentication
- Watch for suspicious emails or SMS messages
- Verify communications claiming to be from Baydöner
Consumers should remain cautious of phishing attempts leveraging breach-related fear tactics. 🔐
Conclusion: A Wake-Up Call for Digital Consumer Protection
The alleged Baydöner data breach underscores a growing cybersecurity reality: consumer-facing businesses are increasingly prime targets for cybercriminal operations. Whether confirmed or not, incidents like this emphasize the importance of proactive monitoring, layered defense strategies, and rapid incident response readiness.
As seen in both this case and the previously analyzed HungryRush exposure, attackers exploit valuable customer ecosystems where identity and behavioral data intersect. Organizations that invest in intelligence-driven defense and continuous monitoring dramatically reduce long-term risk exposure.
Cyber resilience today depends not only on preventing attacks but also on detecting threats beyond organizational boundaries.
👉 Discover much more in our complete guide
👉 Request a demo NOW
Disclaimer: Spoofguard reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
