➤Summary
Data breach alert: a newly surfaced claim on the dark web suggests a massive exposure of customer data tied to russellcellular.com. According to a post published on March 17, 2026, on Darkforums.st by a user known as “Sorb,” a database allegedly containing over 6.3 million customer records has been leaked. The dataset, reportedly discovered by the Kaduu team during routine monitoring, includes highly sensitive personal and device-related information. If verified, this cybersecurity incident could have serious implications for both individuals and the broader telecom ecosystem. In this spoofguard.io article, we break down what is known, the potential risks, and how businesses can strengthen their defenses using modern brand protection strategies 🔐.
What Happened in the Alleged Russell Cellular Data Breach
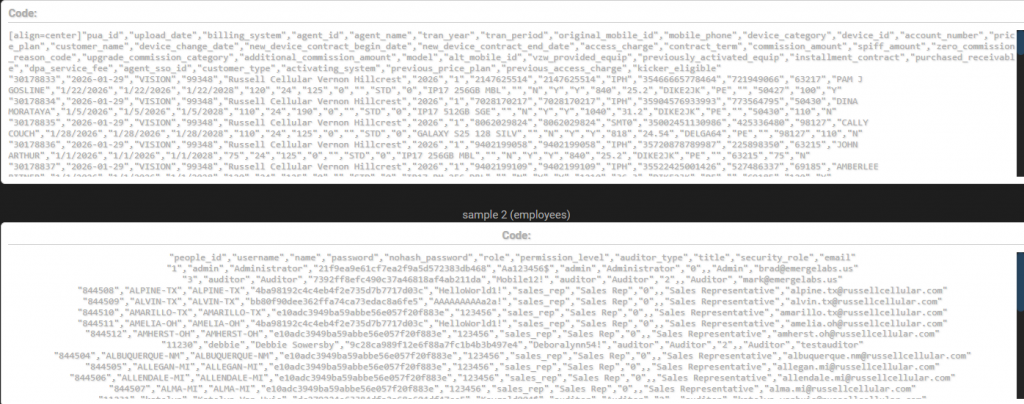
The alleged Russell Cellular data breach revolves around a database export shared in CSV format totaling approximately 61 GB. According to the forum post, the dataset includes 209 tables and covers a wide range of customer and operational data. The exposure reportedly affects more than 6,300,000 unique customer records, excluding duplicate entries.
The author claims multiple attempts were made to contact the company, including reaching out to support teams and employees, but no response was received. This lack of acknowledgment, if accurate, raises concerns about incident response readiness and communication protocols.
The Kaduu team identified the leak through dark web monitoring, highlighting the importance of automating the process from domain monitoring to detect threats early 🕵️♂️.
Types of Compromised Data
The leaked dataset allegedly contains a wide array of sensitive information. Here is a clear breakdown:
| Data Type | Description |
| Full Name | Customer identification |
| Phone Number | Contact details |
| ESN Number | Device identifier |
| IMEI/SN Number | Unique device tracking |
| Account Number | Customer account reference |
| Invoice Number | Billing records |
| Tracking Number | Shipment details |
| Contract Number | Service agreements |
| Device/Plan Info | Purchased phones, upgrades, tariffs |
This combination of personal data and device identifiers significantly increases the risk of identity theft, SIM swapping, and fraud 📱.
Why This Leak Is Particularly Dangerous
Unlike typical breaches that expose only basic personal data, this incident allegedly includes device-level identifiers such as IMEI and ESN numbers. These elements can be exploited for:
- Device cloning
- Unauthorized network access
- Targeted phishing attacks
- Fraudulent warranty claims
The inclusion of contract and billing data further amplifies the risk, enabling attackers to build highly detailed victim profiles.
Question: Why are IMEI and ESN numbers critical in a data breach?
Answer: Because they uniquely identify a device, allowing attackers to impersonate or manipulate telecom services tied to that device.
The Role of Dark Web Monitoring in Early Detection
This incident underscores the importance of proactive cybersecurity measures like dark web intelligence. The Kaduu team discovered the database during routine monitoring, demonstrating how early detection can mitigate damage.
Organizations should consider implementing solutions that support:
- Continuous threat intelligence
- Automated alerts
- Domain spoofing protection
- Brand protection strategies
Platforms like SpoofGuard provide tools for detecting impersonation domains and preventing misuse of brand identity.
These solutions help companies stay ahead of cybercriminals and reduce exposure risks.
Cybersecurity Risks for Customers and Businesses
The Russell Cellular data breach could lead to multiple downstream threats:
- Identity theft and financial fraud 💳
- SIM swapping attacks
- Phishing campaigns using real customer data
- Unauthorized account access
From a business perspective, the consequences may include:
- Reputational damage
- Regulatory penalties
- Loss of customer trust
- Operational disruption
According to the National Institute of Standards and Technology (NIST), organizations must adopt layered security approaches to mitigate such risks (https://www.nist.gov).
Practical Checklist: How to Protect Against Data Breaches
Here’s a quick checklist to reduce exposure and improve resilience:
- Enable multi-factor authentication (MFA)
- Monitor accounts for unusual activity
- Avoid sharing device identifiers publicly
- Use domain spoofing protection tools
- Automate the process from domain monitoring
- Educate employees on phishing risks
- Implement brand protection strategies
💡 Practical tip: Businesses should integrate automated monitoring systems that scan for leaked data and suspicious domain registrations in real time.
The Importance of Brand Protection Strategies
A key takeaway from this data breach alert is the need for robust brand protection. Cybercriminals often exploit leaked data to impersonate companies and deceive customers.
Effective brand protection strategies include:
- Monitoring domain registrations similar to your brand
- Detecting phishing websites early
- Securing email channels against spoofing
- Leveraging AI-driven threat detection
By combining these measures, organizations can significantly reduce the likelihood of follow-up attacks after a breach 🛡️.
What Companies Should Do Next
If the allegations are confirmed, immediate actions should include:
- Conducting a full forensic investigation
- Notifying affected customers
- Strengthening security infrastructure
- Collaborating with cybersecurity experts
Transparency and rapid response are critical to minimizing damage and rebuilding trust.
Conclusion
The alleged Russell Cellular data breach serves as a stark reminder of the evolving cybersecurity landscape. With millions of records potentially exposed, the incident highlights the urgent need for proactive defenses, including automating the process from domain monitoring, implementing domain spoofing protection, and adopting comprehensive brand protection strategies. Businesses must act quickly to detect threats, protect customers, and secure their digital assets.
Discover much more in our complete guide
Request a demo NOW
Disclaimer: Spoofguard reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
