➤Summary
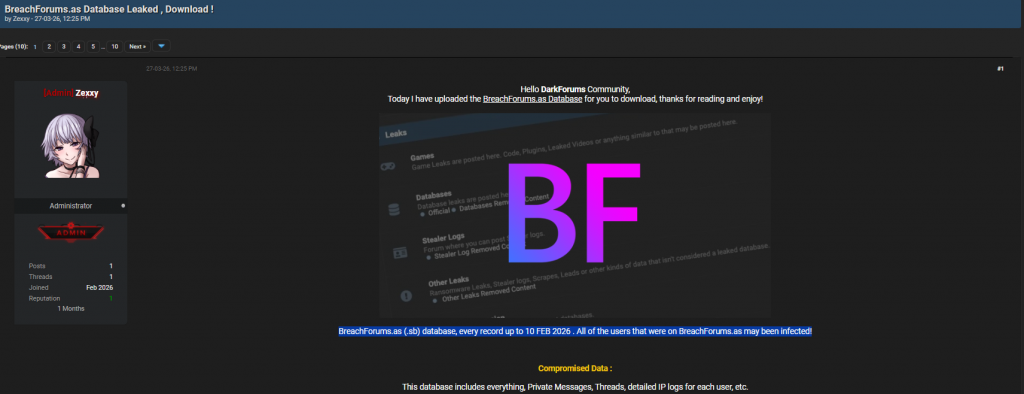
The alleged BreachForums.as database leak has sparked serious discussion across cybersecurity communities, highlighting why domain monitoring software has become essential for organizations protecting their digital identity. According to a post published on Darkforums by the author “Zexxy,” the breach allegedly exposed user records dating up to February 10, 2026, potentially affecting thousands of forum users.
Cybercriminal forums have historically served as hubs for leaked credentials, threat coordination, and underground intelligence exchanges. When such platforms themselves become compromised, the risks extend beyond individual accounts into wider cyber-threat ecosystems. Businesses relying on proactive monitoring, threat intelligence, and brand protection strategies now face renewed urgency to detect impersonation, phishing domains, and credential leaks before attackers weaponize them. 🚨
This spoofguard.io article analyzes the alleged leak, what data may have been exposed, and how companies can mitigate risks using modern security solutions like a domain monitoring service and the best brand protection software available today.
Overview of the Alleged BreachForums.as Database Leak
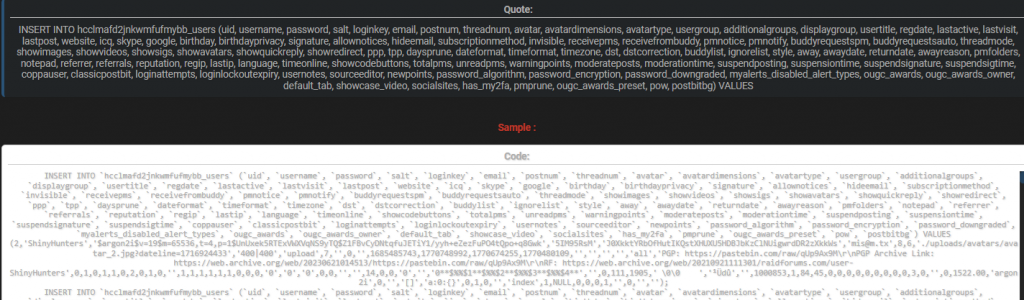
The forum post claims that the BreachForums.as (.sb) database was leaked, including records up to early February 2026. The dataset allegedly contains structured SQL entries referencing a MyBB user table (hcclmafd2jnkwmfufmybb_users) with extensive account metadata.
Compromised fields reportedly include:
- User IDs and usernames
- Password hashes (argon2i algorithm)
- Email addresses
- Login keys and salts
- Registration and last activity timestamps
- IP address data
- Private profile configurations
- Messaging and notification preferences
One example record references a well-known threat actor alias, suggesting high-profile accounts may have been included. While authenticity has not been independently verified, cybersecurity analysts treat such claims seriously due to the platform’s historical association with data trading communities.
The author further claimed that “all users may have been infected,” implying possible malware distribution or credential harvesting risks. Even if exaggerated, such statements underline the importance of cyber threat monitoring and early detection systems.
Why This Leak Matters Beyond a Single Forum
Data breaches affecting cybercrime forums create ripple effects across the internet. Unlike traditional breaches, attacker communities often reuse infrastructure, aliases, and credentials across multiple services.
Potential impacts include:
- Exposure of operational identities
- Increased phishing campaigns
- Credential reuse attacks
- Expansion of underground intelligence networks
Organizations must understand that leaked forum data frequently becomes fuel for automated attacks. Threat actors analyze datasets to identify targets, corporate emails, or brand references.
This is where domain monitoring software plays a critical role. By continuously scanning domain registrations and suspicious activity, companies can identify malicious domains created using stolen data or impersonation strategies. 🔎
What Data Exposure Could Enable Attackers to Do
When user databases leak, attackers gain more than login credentials. Structured forum data enables behavioral profiling.
Below is a simplified breakdown:
| Data Type | Possible Risk | Business Impact |
| Emails | Phishing campaigns | Brand impersonation |
| Password hashes | Credential cracking | Account takeover |
| IP logs | Geolocation tracking | Targeted attacks |
| Activity timestamps | Behavioral analysis | Social engineering |
| Profile links | Identity correlation | Reputation damage |
Even encrypted passwords can become vulnerable through offline cracking attempts over time. Combined with dark web monitoring insights, attackers can pivot toward corporate targets connected to exposed users.
A reliable domain monitoring service helps organizations detect newly registered domains mimicking brand assets before attacks escalate.
The Growing Role of Domain Monitoring in Brand Protection
Modern cyber threats rarely begin with direct system intrusion. Instead, attackers often launch phishing domains first.
For example:
- Fake login portals
- Typosquatted domains
- Brand impersonation websites
- Malware distribution landing pages
Advanced domain monitoring software tracks domain registrations globally, analyzing naming patterns linked to trademarks or company names.
According to cybersecurity reporting from , threat actors increasingly rely on automated infrastructure creation, making early detection essential.
Organizations using the best brand protection software gain visibility into: - Newly registered look-alike domains
- DNS changes and suspicious hosting
- SSL certificate anomalies
- Dark web mentions connected to brand names
This proactive approach shifts security from reaction to prevention.
Could Forum Users Really Be “Infected”?
One question frequently asked is:
Does a leaked database automatically mean users were infected with malware?
Short answer: No — but the risk increases significantly.
A database leak alone does not deploy malware. However, attackers may use exposed information to deliver targeted phishing or malicious downloads later.
Common follow-up attacks include:
- Personalized phishing emails
- Fake password reset requests
- Malware disguised as forum updates
- Credential stuffing campaigns
Organizations monitoring digital threats using a domain monitoring service can detect phishing infrastructure early and block access before employees interact with malicious content. 🛡️
Indicators Organizations Should Watch Immediately
Security teams should monitor for warning signs linked to leaked community databases:
- Sudden spikes in phishing emails referencing breaches
- Newly registered domains containing brand keywords
- Credential leak alerts tied to employee emails
- Unusual login attempts across corporate platforms
- Increased spoofed sender domains
These indicators often appear within days or weeks after a publicized breach claim.
Digital risk protection tools integrated with domain monitoring software help automate these checks continuously rather than relying on manual analysis.
Practical Security Checklist After a Major Leak
Here is a quick response checklist companies should follow:
✅ Audit employee credential exposure through breach monitoring
✅ Enforce password resets and enable MFA
✅ Monitor new domain registrations globally
✅ Deploy phishing detection filters
✅ Review brand impersonation alerts
✅ Strengthen DNS monitoring policies
A practical tip: organizations should combine threat intelligence feeds with automated domain surveillance rather than relying solely on endpoint security tools. Prevention happens outside your network perimeter. ⚠️
How Brand Protection Platforms Reduce Exposure
The best brand protection software combines several security layers into a unified system:
- Domain monitoring
- Dark web intelligence
- Social media impersonation detection
- Phishing site analysis
- Automated takedown workflows
Solutions like those offered by focus specifically on identifying malicious domains targeting organizations before customers encounter them.
Businesses increasingly adopt integrated domain monitoring service platforms because attackers now automate domain creation at scale. Manual tracking is no longer feasible.
Cybersecurity expert Bruce Schneier once noted: “Security is a process, not a product.” Continuous monitoring reflects this philosophy by adapting defenses as threats evolve.
Why Domain Monitoring Is Now a Business Priority
From an operational perspective, domain abuse directly affects:
- Customer trust
- Search engine reputation
- Email deliverability
- Brand credibility
Phishing domains indexed by search engines can harm visibility and user confidence.
By implementing domain monitoring software, companies gain: - Early threat alerts
- Faster incident response
- Reduced fraud losses
- Improved compliance posture
Organizations exploring proactive protection often begin with a brand protection free trial to evaluate detection capabilities before full deployment.
Real-World Scenario: How Attacks Typically Unfold
A typical attack chain after a database leak looks like this:
- Data appears on underground forums
- Threat actors analyze exposed emails
- Look-alike domains are registered
- Phishing campaigns launch
- Credentials harvested from victims
- Corporate systems targeted
Without automated monitoring, companies often discover attacks only after customers report fraud.
A robust domain monitoring service identifies suspicious domain registrations during stage three — stopping attacks before damage occurs. 🚀
How SpoofGuard.io Helps Organizations Stay Protected
Organizations seeking proactive protection can leverage tools available at to detect threats tied to brand abuse and leaked data ecosystems.
Key capabilities include:
- Continuous domain surveillance
- Threat intelligence correlation
- Automated alerts and reporting
- Phishing detection powered by AI
- Brand impersonation tracking
Companies evaluating security improvements often request brand protection demo access to understand how monitoring integrates into existing workflows.
The combination of automation and intelligence makes modern platforms significantly more effective than traditional reactive defenses.
Final Thoughts: Lessons From the Alleged BreachForums.as Leak
Whether fully verified or partially exaggerated, the alleged BreachForums.as database leak reinforces a critical cybersecurity truth: breaches rarely remain isolated events. Information spreads quickly across underground networks, enabling follow-up attacks targeting brands, employees, and customers alike.
Organizations that rely solely on firewalls or endpoint security risk missing early warning signals occurring outside their infrastructure. Implementing domain monitoring software alongside a trusted domain monitoring service allows companies to detect threats at their origin — malicious domains.
The growing sophistication of phishing and impersonation campaigns means proactive monitoring is no longer optional but foundational to digital risk protection. 🌐
Discover much more in our complete guide
Request a demo NOW
Disclaimer: Spoofguard reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
