➤Summary
Protect your brand in real time with SpoofGuard. Detect impersonation and phishing attempts before they cause harm with automated takedown.
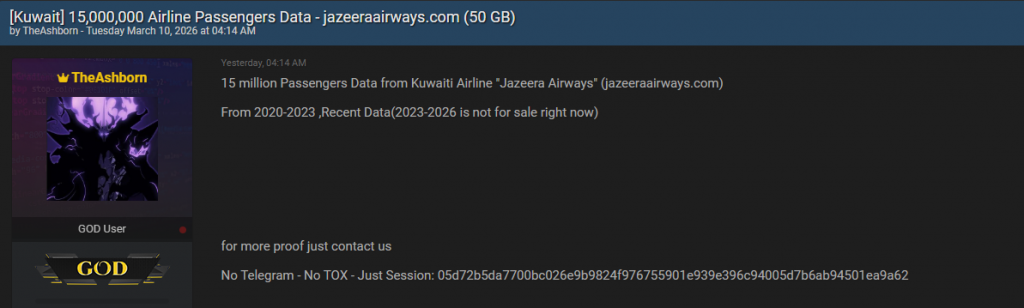
Request a demo →The Jazeera Airways data leak has quickly become one of the most discussed cybersecurity incidents in aviation during 2026. On March 10, 2026, a post published on Breachforums.as by a user known as TheAshborn claimed the sale of data belonging to approximately 15 million airline passengers linked to jazeeraairways.com. According to the forum post, the dataset covers passenger records collected between 2020 and 2023 and allegedly originated from a zero-day exploit. While the airline has not publicly confirmed the claims at the time of writing, cybersecurity analysts are already evaluating the potential scale of exposure and the risks to travelers worldwide. ✈️
This spoofguard.io article examines what is currently known, why the alleged airline data breach matters, and how organizations and passengers can reduce risks tied to large-scale data exposure incidents.
Timeline of the Alleged Breach Incident
The forum publication states that the data originates from historical airline systems rather than recent operational databases. Key claims include:
- Dataset allegedly includes passenger information from 2020–2023.
- Newer data (2023–2026) was reportedly not offered for sale.
- The attacker claimed exploitation of a previously unknown vulnerability.
- Data listing appeared on BreachForums on March 10, 2026.
Although unverified, incidents following similar patterns have historically led to credential abuse, identity fraud attempts, and targeted cyber campaigns. The alleged Jazeera Airways data leak therefore raises immediate concerns for aviation cybersecurity professionals and regulators.
Cybersecurity researchers often emphasize that early forum listings serve as warning signals rather than confirmed facts. As noted by analysts referenced by the Cybersecurity and Infrastructure Security Agency, organizations must treat such disclosures seriously even before official confirmation.
What Data May Have Been Exposed?
The author of the forum post did not publish full samples publicly, but claims suggest typical airline passenger datasets. These commonly include:
| Data Category | Potential Risk |
| Full names | Identity theft |
| Booking details | Travel profiling |
| Contact information | Social engineering |
| Passport or ID references | Fraud attempts |
| Loyalty program data | Account takeover |
Such passenger information becomes especially valuable when combined with other leaked datasets circulating online. This transforms a single airline data breach into a broader ecosystem risk affecting digital identity protection. 🔐
Why a Zero-Day Exploit Matters
A zero-day exploit refers to a vulnerability unknown to the vendor at the time of exploitation. If verified, this would mean attackers accessed systems before patches or defensive signatures existed.
Why is this significant?
- Traditional antivirus systems may not detect the intrusion.
- Attackers can remain undetected longer.
- Historical databases are often targeted due to weaker monitoring.
The Jazeera Airways data leak claim highlights how legacy systems storing archived passenger information can become attractive targets. Aviation companies frequently maintain long-term travel records for operational and regulatory reasons, making them high-value repositories.
Understanding the Broader Airline Data Breach Trend
The aviation industry has faced growing cybersecurity pressure over the last decade. Airlines manage vast ecosystems including booking platforms, mobile apps, payment processors, and partner integrations.
Common attack vectors include:
- Credential stuffing
- API vulnerabilities
- Cloud misconfigurations
- Third-party vendor compromise
Experts warn that aviation cybersecurity risks extend beyond airlines themselves. Travel agencies, payment gateways, and loyalty platforms can all introduce exposure points.
One emerging threat linked to incidents like this involves Phishing websites impersonating airline portals to harvest login credentials after breaches become public knowledge. 🎯
Possible Risks for Affected Passengers
If the allegations prove accurate, passengers could face several consequences:
- Targeted phishing campaigns referencing real travel history.
- Fraudulent travel confirmations or refund scams.
- Account takeover attempts using personal identifiers.
- Increased identity theft risk across financial services.
Question: Can leaked airline data really be dangerous even without credit card numbers?
Answer: Yes. Personal travel data enables highly convincing social engineering attacks, which often succeed without financial information.
Threat actors frequently combine exposed booking data with brand and logo spoofing techniques to make fraudulent emails appear legitimate, increasing success rates.
How Attackers Monetize Passenger Data
Unlike financial breaches focused on immediate theft, passenger datasets offer long-term value. Criminal marketplaces use such information for:
- Personalized scam campaigns
- Travel-themed fraud operations
- Dark web identity bundles
- Corporate espionage targeting frequent business travelers
Cybercriminal groups increasingly rely on layered exploitation models rather than quick resale. The alleged Jazeera Airways data leak could therefore remain relevant months or years after initial exposure.
Detection Challenges and Website Security Concerns
Airline platforms are complex environments integrating booking engines, customer portals, and content management systems. Attackers sometimes manipulate frontend elements to maintain persistence.
Security teams increasingly perform Website Content Changes and Risk Analysis to detect unauthorized modifications that signal deeper compromise.
Monitoring solutions capable of identifying abnormal page behavior or unauthorized scripts are becoming essential for aviation organizations seeking early detection.
Companies exploring preventive monitoring tools can review solutions offered at spoofguard.io to strengthen website integrity monitoring and brand protection.
Practical Checklist: How Passengers Can Protect Themselves
If you suspect your data may be involved in an airline data breach, follow this checklist:
✅ Change airline and travel account passwords immediately
✅ Enable multi-factor authentication wherever available
✅ Monitor travel confirmation emails carefully
✅ Avoid clicking links in unsolicited airline messages
✅ Check loyalty accounts for unusual activity
✅ Use credit monitoring services if identity data may be exposed
A proactive approach significantly reduces risk even when exposure cannot be reversed. 🛡️
Organizational Lessons for the Aviation Industry
Whether confirmed or not, the alleged incident provides important lessons:
- Archive systems require equal security monitoring.
- Vulnerability management must include third-party integrations.
- Threat intelligence monitoring of underground forums is critical.
- Brand protection should extend beyond infrastructure security.
Airlines must also anticipate post-breach exploitation campaigns. Attackers frequently launch fake customer support portals or imitation login pages shortly after breach news spreads.
Organizations looking to strengthen proactive defenses can explore threat detection resources at https://spoofguard.io/ for monitoring suspicious domain activity and impersonation attempts.
The Role of Threat Intelligence and Monitoring
Modern cybersecurity relies heavily on early intelligence signals. Forum disclosures like the one attributed to TheAshborn often provide:
- Indicators of compromise
- Attack methodology hints
- Data scope estimates
- Timing insights for response teams
Continuous monitoring of dark web environments allows companies to react before large-scale abuse occurs. The Jazeera Airways data leak discussion demonstrates how public underground posts can trigger defensive action even without official breach confirmation.
Industry experts recommend combining intelligence feeds with automated monitoring to detect malicious domains imitating airline brands. More insights about proactive brand monitoring strategies are available at Spoofguard.io
Expert Perspective on Aviation Cybersecurity
Aviation cybersecurity consultant Mark Henderson once noted:
“Airlines hold behavioral data as valuable as financial records. Attackers exploit trust, not just technology.”
This statement reflects why passenger information exposure often leads to secondary attacks rather than immediate financial theft.
The alleged 15 million airline passenger data breach scenario reinforces the need for layered security — combining infrastructure defense, monitoring, and customer awareness.
What Happens Next?
Several outcomes may follow:
- Official confirmation or denial from the airline.
- Independent security investigations.
- Regulatory inquiries depending on jurisdiction.
- Increased scam activity targeting travelers.
Passengers should remain cautious but avoid panic until verified disclosures emerge. Monitoring official airline communications remains the safest approach.
Conclusion: Why Awareness Matters Now
The alleged Jazeera Airways data leak serves as a powerful reminder that aviation cybersecurity risks continue to evolve alongside digital transformation. Even unverified breach claims can trigger real-world threats when attackers leverage stolen narratives to deceive users. Understanding how airline data breaches operate helps passengers recognize warning signs and helps organizations strengthen defenses before damage escalates. 🌐
Cybersecurity today is no longer only about preventing intrusion—it is about detecting misuse, protecting brand trust, and educating users against increasingly sophisticated scams. Staying informed and proactive is the strongest defense against modern data exposure risks. 🚨
Discover much more in our complete guide
Request a demo NOW
Disclaimer: Spoofguard reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
SpoofGuard detects domain impersonation and phishing threats in real time. Don’t wait until damage is done.
Request a demo →