➤Summary
Protect your brand in real time with SpoofGuard. Detect impersonation and phishing attempts before they cause harm with automated takedown.
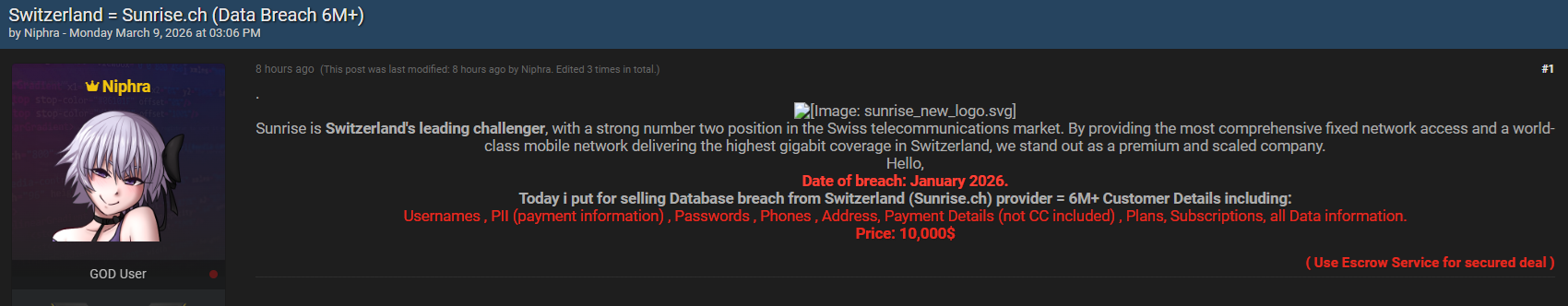
Request a demo →The Sunrise data breach has recently surfaced as an alleged cybersecurity incident discussed on a well-known underground forum, raising concerns across Europe’s telecommunications sector. According to a post published on breachforums.as by a threat actor identified as “Niphra” on March 9, 2026, a database containing more than six million customer records linked to Switzerland’s Sunrise.ch platform is reportedly being offered for sale. The breach allegedly occurred in January 2026 and includes sensitive user information such as usernames, personal identifiable information (PII), phone numbers, addresses, subscriptions, and payment-related details. While the claims remain unverified at the time of writing, the scale and nature of the data described have sparked serious discussion among cybersecurity analysts and privacy advocates ⚠️. This spoofguard.io article analyzes what is known, the risks involved, and how organizations and individuals should respond to such incidents.
Overview of the Alleged Sunrise.ch Incident
The alleged incident describes a massive telecom data exposure involving Sunrise customers. The forum listing claims that attackers accessed a wide dataset tied to customer accounts, including login credentials and service information. The database is reportedly listed for sale at a price of $10,000, suggesting potential intent for resale, fraud operations, or credential-stuffing campaigns.
According to the forum description, exposed records may include:
- Usernames and encrypted passwords
- Phone numbers and addresses
- Subscription plans and service details
- Payment information (excluding credit card numbers)
- Account metadata and customer identifiers
If confirmed, this would classify as a large-scale telecom data breach, a category increasingly targeted due to the high value of identity-linked datasets. Telecommunications providers hold extensive customer records, making them attractive targets for cybercriminal groups seeking monetizable information 🔎.
Timeline and Context of the Leak
The forum post indicates the breach occurred in January 2026, though publication only appeared in March. This delay is typical in underground markets, where threat actors first validate datasets or negotiate private sales before public listings.
Cybersecurity researchers often observe three phases in such incidents:
- Initial intrusion and data extraction
- Private circulation among threat actors
- Public marketplace listing or auction
The alleged Sunrise data breach appears to have entered the third phase. At this stage, risks increase significantly because multiple buyers may gain access simultaneously.
Industry reports from organizations like IBM Security highlight that stolen datasets frequently circulate for weeks before detection or disclosure, increasing exposure risk for affected users. More details on breach lifecycle analysis can be found via IBM’s cybersecurity research hub: https://www.ibm.com/security/data-breach.
What Data Was Allegedly Compromised?
Understanding the type of information involved helps assess potential impact. Based on the listing description, the compromised dataset includes several sensitive categories.
| Data Category | Risk Level | Possible Abuse |
| Usernames & passwords | High | Account takeover |
| Phone numbers | Medium | SIM swapping scams |
| Addresses | Medium | Identity fraud |
| Subscription plans | Low–Medium | Social engineering |
| Payment metadata | High | Fraud profiling |
| Unlike breaches involving full credit card details, payment data without card numbers still carries significant risk because it helps attackers build identity profiles. Combined information allows criminals to impersonate customers when contacting service providers 📱. |
Why Telecom Companies Are Frequent Targets
Telecommunications providers store interconnected datasets combining identity, billing, and communication records. This aggregation creates a high-value environment for attackers.
Common motivations behind telecom breaches include:
- Identity theft operations
- SIM swap attacks
- Credential reuse exploitation
- Large-scale phishing campaigns
A telecom data breach can also enable cross-platform attacks because many users reuse passwords across services.
Cybersecurity analysts emphasize that telecom databases often act as “identity anchors,” meaning compromised information can unlock access to banking, email, and social media accounts.
How the Data May Be Used on Underground Markets
When a dataset appears for sale, buyers typically fall into distinct categories:
- Fraud groups seeking verified identities
- Phishing operators targeting specific regions
- Data brokers aggregating leaked datasets
- Credential-stuffing attackers testing reused passwords
The relatively low asking price compared to dataset size suggests volume monetization rather than exclusivity. Large datasets are sometimes intentionally priced lower to encourage rapid distribution.
For insights into how underground listings evolve, readers can explore threat intelligence analysis published at darknetsearch.com, which tracks emerging breach activity patterns and marketplace trends.
Key Risks for Customers and Businesses
The alleged Sunrise data breach introduces several immediate and long-term risks.
First, credential reuse remains the biggest threat. Even hashed passwords can sometimes be cracked or used in automated login attempts.
Second, targeted phishing becomes easier. Attackers equipped with subscription details can craft convincing messages referencing real services.
Third, identity correlation attacks may occur, where multiple leaks are combined to create detailed victim profiles.
Fourth, telecom impersonation scams could rise, especially through SMS or phone calls appearing legitimate 📩.
Question: Can attackers cause harm even without credit card numbers?
Answer: Yes. Personal information combined with account details enables identity fraud, social engineering, and account takeovers without needing full payment credentials.
Indicators That Suggest a Legitimate Breach
Not every dark web listing reflects a real incident. Analysts typically verify claims using several indicators:
- Sample data validation
- Cross-reference with known customers
- Metadata consistency checks
- Unique dataset markers
- Independent researcher confirmation
Until independent validation occurs, the Sunrise data breach should be considered an alleged incident rather than confirmed exposure.
The Role of Cyber Threat Intelligence
Threat intelligence teams continuously monitor underground communities to identify early warning signals. Proactive monitoring allows organizations to respond before widespread exploitation occurs.
Security professionals often rely on specialized platforms performing deep forum tracking, credential indexing, and automated leak detection. Continuous analysis published on https://darknetsearch.com/ helps organizations understand evolving attacker behaviors and exposure risks.
According to cybersecurity experts, early detection reduces breach impact significantly because password resets and alerts can occur before criminals operationalize stolen data.
Practical Checklist: How Users Can Protect Themselves
If you suspect your information may be involved in a telecom data breach, follow this checklist ✅:
- Change passwords immediately, especially reused ones
- Enable multi-factor authentication (MFA)
- Monitor telecom account activity
- Watch for suspicious SMS or calls
- Review billing statements regularly
- Avoid clicking unexpected service notifications
Organizations should complement user awareness with a Dark web monitoring report, Domain Monitoring, Infrastructure Monitoring, spoofing prevention, integrated into their broader security strategy.
Organizational Lessons From the Incident
Even alleged incidents provide valuable cybersecurity lessons. Telecom providers must continuously strengthen defenses against modern threats.
Key best practices include:
- Zero-trust access architecture
- Continuous vulnerability scanning
- Privileged access monitoring
- Data segmentation and encryption
- Incident response simulation exercises
An expert from the European cybersecurity community once noted: “Breaches rarely begin with sophisticated attacks—they begin with overlooked exposure points.” This insight highlights why proactive risk management matters more than reactive remediation 🛡️.
Broader Industry Impact
If validated, the Sunrise data breach could influence regulatory discussions across Europe. Telecommunications companies operate under strict data protection frameworks such as GDPR, which impose reporting and notification obligations.
Large breaches often trigger:
- Regulatory investigations
- Customer notification campaigns
- Increased compliance audits
- Security investment acceleration
The telecom sector has already experienced rising attack frequency, driven by expanding digital services and cloud integrations.
Long-Term Implications for Cybersecurity Trends
The alleged Sunrise.ch customer database leak illustrates a broader shift toward identity-centric cybercrime. Attackers increasingly target aggregated datasets instead of financial systems directly.
Emerging trends include:
- Data aggregation marketplaces
- Subscription-based cybercrime services
- Automated identity exploitation tools
- AI-assisted phishing campaigns 🤖
These developments emphasize the importance of early detection rather than post-breach response.
Organizations investing in continuous monitoring and threat intelligence typically reduce incident response costs and reputational damage.
Conclusion: Staying Ahead of Emerging Data Breaches
Whether confirmed or not, the Sunrise data breach demonstrates how quickly sensitive information can appear in underground marketplaces and potentially reach malicious actors worldwide. Users should treat such reports as reminders to strengthen personal cybersecurity hygiene, while organizations must invest in proactive monitoring and layered defenses.
Cyber threats continue evolving, but awareness and preparation remain powerful defenses. Staying informed through reliable intelligence platforms and implementing preventive strategies helps reduce exposure risks and protects digital identities over time 🔐.
Discover much more in our complete guide
Request a demo NOW
Disclaimer: Spoofguard reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
SpoofGuard detects domain impersonation and phishing threats in real time. Don’t wait until damage is done.
Request a demo →