➤Summary
The Pernambuco data breach stands as one of the most alarming cybersecurity incidents of late 2025. In December, a user known as “0x0dayToDay” published a massive dataset on a criminal forum, exposing over 9.1 million records tied to citizens of Pernambuco, Brazil. This leak included highly sensitive personal information such as identification numbers, contact details, and residential data, raising serious concerns about privacy and national data protection frameworks. As organizations increasingly rely on digital infrastructures, incidents like this highlight the urgent need for proactive solutions like a threat intelligence platform and advanced monitoring tools. Understanding what happened, what data was exposed, and how to mitigate risks is critical for enterprises and individuals alike in today’s evolving threat landscape. 🚨
What Happened in the Pernambuco Breach?
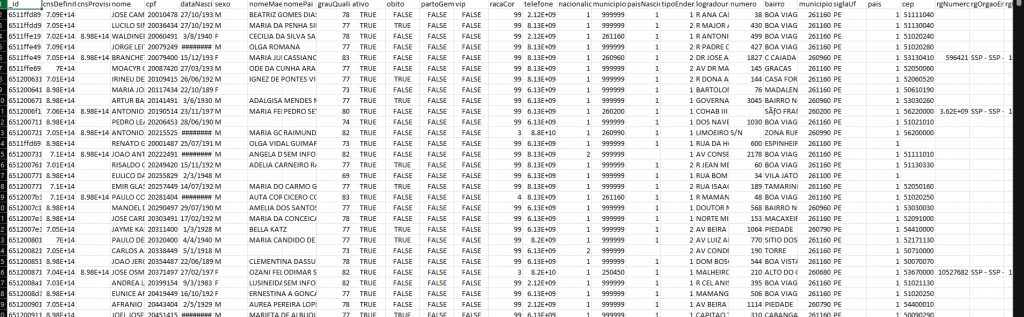
The Pernambuco data breach originated from a post on BreachForums, where the attacker claimed to release 9,190,832 data entries. According to reports, the dataset included fields such as _id, nome, cpf, dataNascimento, telefone, and even “email[0].email” and “email[1].email”. This structured database suggests a highly organized extraction, possibly from a government or healthcare-related system.
Authorities were alerted shortly after the publication, and the state government confirmed the incident while attributing responsibility to federal systems. The scale of this exposure makes it one of the largest regional leaks in Brazil’s history.
The leaked dataset is particularly concerning due to its depth and variety. Below is a simplified breakdown of the compromised data fields:
- Personal identification: CPF, RG number, CNS identifiers
- Demographics: name, date of birth, gender, ethnicity
- Family details: mother’s and father’s names
- Contact information: phone numbers and email addresses
- Address data: street, city, postal code, country
- Sensitive indicators: health-related flags, VIP status, nationality
This level of detail enables identity theft, phishing campaigns, and social engineering attacks at scale. The Pernambuco data breach is not just about quantity—it’s about the quality and usability of the exposed information.
Why This Breach Matters Globally
You might wonder: Is this breach only a local issue in Brazil?
The answer is no. Data leaks of this magnitude have global implications because cybercriminals often aggregate datasets from multiple regions to create detailed identity profiles. These profiles can be used in international fraud schemes, credential stuffing, and targeted attacks.
Organizations worldwide must recognize that a breach in one region can affect users, partners, and systems globally. This is why adopting a threat intelligence platform is no longer optional—it’s essential for anticipating and mitigating cross-border cyber risks. 🌍
The Role of Threat Intelligence in Preventing Similar Attacks
A threat intelligence platform helps organizations detect, analyze, and respond to threats before they escalate into major incidents like the Pernambuco data breach. These platforms gather data from dark web forums, hacker communities, and compromised databases to provide actionable insights.
Key benefits include:
- Early detection of leaked credentials
- Monitoring of suspicious activity across domains
- Real-time alerts for potential threats
- Improved incident response capabilities
By leveraging such tools, companies can stay ahead of attackers and reduce the likelihood of large-scale data exposure. 🔍
Domain Monitoring and Enterprise Protection
Another critical layer of defense is a domain monitoring service. In many breaches, attackers create fake domains to exploit stolen data or impersonate legitimate organizations. A domain monitoring for enterprises solution helps identify these malicious domains early.
For example, if cybercriminals use data from the Pernambuco data breach to launch phishing campaigns, domain monitoring tools can detect and flag suspicious websites before they harm users.
Learn more about proactive protection strategies at Spoofguard.io.
Automated Domain Takedown: A Critical Response Tool
Detection alone is not enough. Once a malicious domain is identified, it must be removed بسرعة. This is where an automated domain takedown service becomes essential.
Such services streamline the process of reporting and removing fraudulent domains, reducing the time attackers have to exploit stolen data. In the context of the Pernambuco data breach, rapid takedown capabilities could significantly limit the spread of phishing campaigns and identity fraud. ⚡
Practical Checklist: How to Protect Against Data Breaches
To minimize the impact of incidents like the Pernambuco data breach, organizations should follow this checklist:
- Implement a threat intelligence platform for continuous monitoring
- Use a domain monitoring service to detect fake domains
- Enable multi-factor authentication across all systems
- Regularly audit and update security protocols
- Educate employees about phishing and social engineering
- Deploy an automated domain takedown service for rapid response
This proactive approach can significantly reduce vulnerabilities and improve resilience against cyber threats. ✅
Expert Insight
Cybersecurity analysts often emphasize that “data breaches are not a matter of if, but when.” The Pernambuco data breach illustrates how even large-scale systems can be compromised. Experts recommend integrating intelligence-driven security measures rather than relying solely on reactive defenses.
Conclusion: Turning Lessons into Action
The Pernambuco data breach is a stark reminder of the risks associated with large-scale data storage and inadequate protection measures. With over 9 million records exposed, the incident underscores the importance of adopting advanced cybersecurity solutions such as a threat intelligence platform, domain monitoring for enterprises, and an automated domain takedown service.
Organizations must act decisively to protect their data, users, and reputation. Waiting until after a breach occurs is no longer a viable strategy in today’s threat landscape.
Discover much more in our complete guide
Request a demo NOW
Disclaimer: Spoofguard reports on publicly available threat-intelligence sources. Inclusion of an organization in an article does not imply confirmed compromise. All claims are attributed to external sources unless explicitly verified.
